What is This Trojan.Viknok virus?
Trojan.Viknok Virus is classified as an extremely dangerous, tricky and stubborn Trojan virus in the world of computer. This infection, created by cyber criminals aim to innocent computer attacking is truly a huge disaster for computer user who suffered it. Usually, it is implanted into some unhealthy websites or links, waiting for unconsciously click of innocent computer users. Once it invades into your computer successfully, the system settings and registry will be modified which can disable your antivirus program. That is the reason why your antivirus can not remove it completely. Besides, did you noticed that your computer turns to slower and slower? It is because that this virus will also take over the limited system resources to affect the performance of your computer. Moreover, this Trojan virus is manipulated by cyber hackers behind which may collect the significant information like your ID numbers, bank account or credit card password in your computer. Finally, one of the reasons why it is extremely dangerous is that Trijan.Viknok Virus can constantly spread from one computer to another by sending malicious e-mail and sharing infected links to your online community.
As dangerous as a disaster, Trojan.Viknok virus should be removed as soon as possible once it is noticed. Since it can’t be deleted by your antivirus program, manual removal could be the most effective way to handle it. Wanna learn how to manually remove this nasty Trojan.Viknok virus safely and absolutely, follow this post.Damages of Trojan.Viknok Virus:
1. It invades system without any permission
2. It has bad reputation & impact online3. It spreads to removable drives and other PCs quickly
4. It may bring along all kinds of spyware program
Manual Trojan.Viknok Virus Removal Guide:
1. To stop all Trojan.Viknok Virus processes, press CTRL+ALT+DELETE to open the Windows Task Manager.
%Windir%\temp\random.exe
%Windir%\Temp\random
HKLM|HKCU]\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit
HKLM|HKCU]\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\random
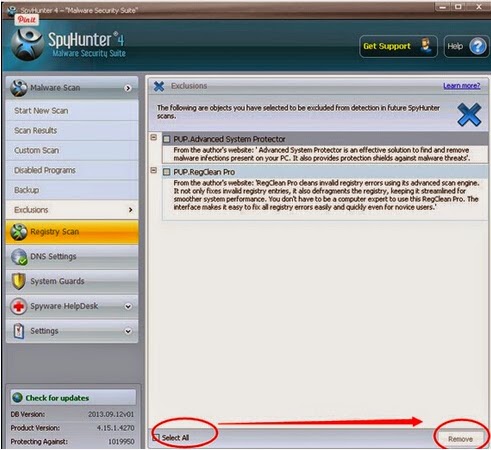
1. Download Spyhunter into your computer by clicking this icon;
2. After you finished installation, you need to run a full scan with it;

3. Select all threats on the list and choose to remove.



No comments:
Post a Comment